Comprehensive Walkthrough on Cybersecurity Education: A Path to Thriving in the Cybersecurity Sector
In the modern digital landscape, cybersecurity isn't an option—it's a must-have. With companies relying heavily on cloud systems, remote work, and digital transactions, the cyber threat landscape has never been more expansive and complex. Cyber criminals aren't just targeting personal data or intellectual property anymore; they're going after critical infrastructure and national security systems too.
As these threats surge, the demand for skilled cybersecurity professionals skyrockets. Organizations across sectors, such as finance, healthcare, government, education, and technology, are actively hunting for individuals who can identify risks, implement defenses, and respond swiftly to incidents. In fact, there's a staggering gap of over 3 million unfilled cybersecurity jobs worldwide, and this number keeps growing year after year.
Whether you're starting a new career, transitioning from tech, or simply possessing a fervent desire to protect digital systems, the cybersecurity field is ready and waiting for a wide variety of talents. But the first essential step is cybersecurity training. This comprehensive guide will walk you through everything you need to understand to get started, from the importance of training in today's job market to the core skills needed, coveted certifications, and expected roles and salaries. So whether your ambition lies in becoming a security analyst, ethical hacker, cloud security engineer, or even a chief information security officer (CISO), this guide sets the foundation for your successful journey into cybersecurity.
The Significance of Cybersecurity Training
Cybersecurity shields systems, networks, and data from cyber threats like malware, ransomware, phishing, and data breaches. From global corporations to small businesses, and even government agencies, everyone needs cybersecurity barriers in place. But it's the people behind these tools and policies that truly make the difference. This is where cybersecurity training plays a pivotal role, developing the talent that underpins digital security defenses.
Key Benefits of Cybersecurity Training
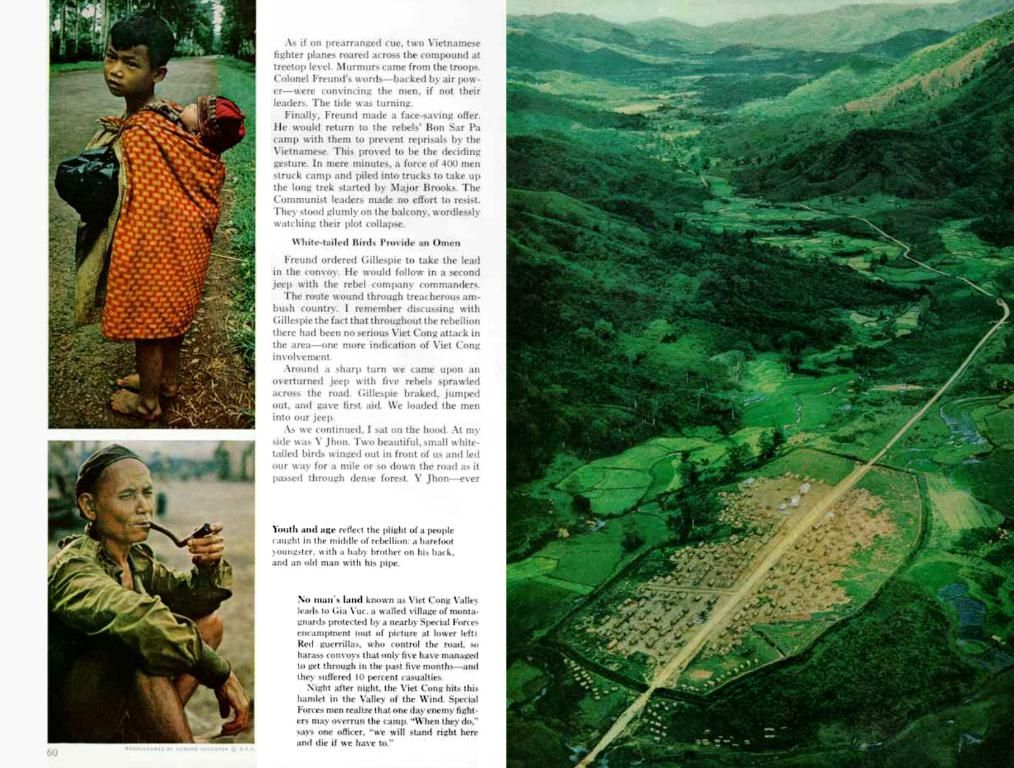
CompTIA Security
- Job Market Advantage: Trained professionals are highly sought after, with over 3 million unfilled cybersecurity jobs globally.
- Lucrative Salaries: Average salaries for cybersecurity roles are significantly higher than many other tech jobs.
- Career Flexibility: Training allows you to pivot into specialties like ethical hacking, forensics, or cloud security.
- Worldwide Relevance: Cybersecurity skills are needed worldwide, providing remote work and international job opportunities.
Beginners
What Cybersecurity Training Covers
$370-$450
Effective training programs are designed to arm you with both theoretical knowledge and hands-on skills. Here are the foundational areas every aspiring cybersecurity professional should master:
Entry
🔐 Core Concepts
- Cyber Threats and Attacks: Learn about malware, phishing, ransomware, and social engineering.
- Information Security Principles: Understand the CIA triad—confidentiality, integrity, and availability—that forms the backbone of cybersecurity.
- Risk Management: Learn how to identify, assess, and mitigate cyber risks.
- Compliance Standards: Get familiar with laws and frameworks like GDPR, HIPAA, ISO 27001, and NIST that regulate cyberspace.
Certified Ethical Hacker (CEH)
⚙️ Technical Skills
Ethical hacking
- Network Security: Master firewalls, intrusion detection/prevention systems, VPNs, and other essential network security tools.
- Operating Systems: Learn the ins and outs of Linux, Windows, and macOS operating systems when it comes to security.
- Cloud Security: Grasp AWS, Azure, and GCP security best practices, as cloud environments continue to dominate the IT landscape.
- Cryptography: Understand encryption, hashing, and secure communications to ensure your data remains private.
- Penetration Testing: Learn how to ethically exploit vulnerabilities using tools like Metasploit.
- SIEM Tools: Get hands-on experience with Splunk, IBM QRadar, or ArcSight for monitoring and alerting.
$950-$1,200
Cybersecurity Specializations
Intermediate
Once you've mastered the fundamentals, you can choose from an array of cybersecurity career paths based on your interests:
- Penetration Tester (Ethical Hacker)
- Security Analyst
- Incident Responder
- Security Architect
- Malware Analyst
- Cloud Security Engineer
- Cybersecurity Consultant
- Chief Information Security Officer (CISO)
Certified Information Systems Security Professional (CISSP)
Each of these roles may require focused training or certifications that align with specific responsibilities.
Leadership, management
Top Cybersecurity Certifications for Career Growth
$749
Certifications validate your skills and make you more appealing in the job market. Here are some of the leading options:
Advanced
| Certification | Best For | Cost Range | Experience Level || --- | --- | --- | --- || CompTIA Security+ | Beginners | $370-$450 | Entry || Certified Ethical Hacker (CEH) | Ethical hacking | $950-$1,200 | Intermediate || Certified Information Systems Security Professional (CISSP) | Leadership, management | $729 | Advanced || Offensive Security Certified Professional (OSCP) | Penetration testing | $1,499 | Intermediate-Advanced || GIAC Security Essentials (GSEC) | General security | $2,000 | Intermediate |
Recommended Training Resources
Offensive Security Certified Professional (OSCP)
📚 Online Learning Platforms
Penetration testing
- Cybrary - Free and premium courses with career paths.
- Coursera - University-led programs from Stanford, IBM, and others.
- Udemy - Affordable training for specific tools or certifications.
- Pluralsight - Excellent for IT professionals expanding into security.
$1,200
👨🏫 Bootcamps and Academies
Intermediate-Advanced
- SANS Institute - Elite cybersecurity training with GIAC certification prep.
- Evolve Security Academy - Hands-on bootcamp with employer connections.
- Springboard - Career coaching and job guarantee for cybersecurity students.
Practical Experience: Why It Matters
GIAC Security Essentials (GSEC)
Hands-on experience is essential in cybersecurity. Recruiters prefer candidates who can demonstrate real-world problem-solving abilities.
General security
Ways to Gain Experience
$2,500
- Labs and Simulations: Practice on platforms like TryHackMe and Hack The Box.
- Internships: Apply for internships with IT departments, security firms, or government agencies.
- Bug Bounty Programs: Participate in ethical hacking competitions to find vulnerabilities in real systems.
- Home Labs: Set up a virtual lab using VirtualBox or VMware to practice pen-testing and incident response scenarios.
Intermediate
Exploring the Main Cybersecurity Domains
Cybersecurity is a broad and multi-faceted discipline with numerous subdomains, each addressing a specific aspect of digital protection. Gaining an understanding of these core domains not only helps newcomers choose a specialization but also builds a comprehensive knowledge base crucial to working across security teams. Below is a breakdown of the main cybersecurity domains, what they cover, and the skills and tools associated with each.
🔌 Network Security
What it is:Network security is the practice of protecting the confidentiality, integrity, and availability of data as it is transmitted across or accessed from networks—both internal and external. This domain is foundational to cybersecurity, as all digital communication depends on networks.
Key Responsibilities:
Entry
- Preventing unauthorized access and attacks like DDoS or Man-in-the-Middle (MITM)
- Monitoring network traffic for anomalies or policy violations
- Implementing network segmentation and access controls
Security Analyst
Common Tools and Technologies:
$65,000 - $85,000
- Firewalls (e.g., Palo Alto, Cisco ASA, pfSense)
- Intrusion Detection/Prevention Systems (IDS/IPS)
- VPNs, proxy servers, and SSL/TLS encryption
- SIEM tools like Splunk or QRadar for monitoring and alerting
Ideal for:Those who enjoy working with infrastructure, routing protocols, and system administration.
Mid
🖥️ Endpoint Security
Security Engineer
What it is:Endpoint security focuses on securing devices like laptops, desktops, mobile phones, and tablets from threats that may originate from inside or outside the organization.
$90,000 - $120,000
Key Responsibilities:
- Deploying antivirus and anti-malware software
- Enforcing device encryption and remote wipe capabilities
- Managing mobile device policies and endpoint detection tools
Advanced
Common Tools and Technologies:
Penetration Tester
- EDR solutions (Endpoint Detection & Response) such as CrowdStrike, SentinelOne, or Microsoft Defender
- Mobile Device Management (MDM) tools like Jamf or Intune
- Patch management systems to ensure devices are up-to-date
$100,000 - $140,000
Ideal for:Professionals interested in hands-on systems management and security monitoring on user-facing devices.
☁️ Cloud Security
Leadership
What it is:As businesses shift to cloud-based environments, cloud security ensures that cloud infrastructure, services, and data remain secure. This includes everything from access management to data storage and compliance.
CISO
Key Responsibilities:
$150,000 - $250,000
- Managing Identity and Access Management (IAM) roles and policies
- Securing workloads in public, private, or hybrid cloud setups
- Monitoring cloud configurations for misconfigurations and vulnerabilities
Common Tools and Technologies:
- Cloud-native tools like AWS IAM, Azure Security Center, GCP Security Command Center
- Cloud Access Security Brokers (CASBs)
- Infrastructure as Code (IaC) scanning tools like Terraform and Checkov
- CSPM (Cloud Security Posture Management) tools such as Prisma Cloud or Wiz
Certifications to Consider:
- AWS Certified Security - Specialty
- Google Professional Cloud Security Engineer
- Microsoft SC-900 or AZ-500
Ideal for:Tech-savvy professionals interested in DevOps, automation, and scalable architectures.
🛡️ Application Security
What it is:Application security (AppSec) is the practice of building secure applications by integrating security into all stages of the software development lifecycle (SDLC). This is crucial in preventing web attacks such as SQL injection, XSS, and RCE.
Key Responsibilities:
- Conducting code reviews and implementing secure development practices
- Identifying and fixing vulnerabilities in software before deployment
- Integrating security testing tools into CI/CD pipelines
Common Tools and Technologies:
- Static Application Security Testing (SAST) tools like SonarQube or Fortify
- Dynamic Application Security Testing (DAST) tools like OWASP ZAP or Burp Suite
- Web Application Firewalls (WAFs) such as Cloudflare or ModSecurity
Certifications to Consider:
- GIAC Web Application Penetration Tester (GWAPT)
- CSSLP (Certified Secure Software Lifecycle Professional)
Ideal for:Developers and engineers with a strong interest in coding and software security.
🔍 Digital Forensics and Incident Response (DFIR)
What it is:This domain focuses on investigating cyber incidents, understanding how a breach occurred, and ensuring that systems are restored while preserving evidence for legal or compliance reasons.
Key Responsibilities:
- Analyzing logs, memory dumps, and disk images to uncover attack vectors
- Maintaining chain of custody for digital evidence
- Conducting post-incident reviews and suggesting remediation
Common Tools and Technologies:
- Forensic tools like Autopsy, EnCase, or FTK
- Incident Response Platforms (IRPs) such as TheHive or Cortex XSOAR
- Log analyzers and packet sniffers like Wireshark and Sysmon
Certifications to Consider:
- GIAC Certified Forensic Analyst (GCFA)
- GIAC Incident Handler (GCIH)
- Certified Incident Handler (ECIH)
Ideal for:Those who are analytical, detail-oriented, and interested in investigative or law enforcement-style work.
⚙️ Bonus Domain: Governance, Risk, and Compliance (GRC)
What it is:Although less technical, GRC professionals play a crucial role in ensuring that organizations comply with cybersecurity laws, industry standards, and internal policies.
Key Responsibilities:
- Performing risk assessments and audits
- Developing security policies and procedures
- Ensuring compliance with regulations like GDPR, HIPAA, or ISO 27001
Common Tools and Frameworks:
- NIST Cybersecurity Framework
- Risk assessment tools like RiskLens
- GRC platforms such as Archer or ServiceNow
Ideal for:Professionals with strong communication and organizational skills, and an interest in policy, law, or business strategy.
Average Salary in Cybersecurity
Cybersecurity offers some of the highest-paying roles in tech. Here's what you can expect based on experience level:
| Level | Title | Average Salary (U.S.) || --- | --- | --- || Entry | Security Analyst | $65,000 - $85,000 || Mid | Security Engineer | $90,000 - $120,000 || Advanced | Penetration Tester | $100,000 - $140,000 || Leadership | CISO | $150,000 - $250,000 |
Salaries may be higher in metropolitan areas like San Francisco, New York, or London, and in industries such as finance, healthcare, and defense.
Cybersecurity Career Outlook
The Bureau of Labor Statistics projects cybersecurity jobs to grow by 35% from 2021 to 2031—much faster than average. The increased adoption of cloud computing, hybrid work environments, and digital transformation is fueling this demand.
In addition, the cybersecurity skills gap means qualified professionals have significant bargaining power when it comes to salary, benefits, and flexibility.
Tips for Success in Cybersecurity
- Stay Updated: Follow news sources like Krebs on Security, DarkReading, and Threatpost.
- Join Communities: Get involved in forums like Reddit's /r/netsec or join cybersecurity Discord servers.
- Build a Portfolio: Document your projects, bug bounties, and certifications in a personal blog or GitHub.
- Network: Attend cybersecurity conferences like DEF CON, RSA Conference, or local BSides events.
- Never Stop Learning: Cybersecurity is dynamic—constant upskilling is the key to staying ahead.
Final Thoughts: Your Cybersecurity Journey Begins Today
Whether you're a student, a career-changer, or an IT professional expanding your skill set, cybersecurity training opens doors to one of the most in-demand and impactful careers of the future. With a blend of theoretical knowledge, practical skills, and the right certifications, you can build a fulfilling, high-paying career defending digital frontiers.
Start small, stay consistent, and never stop learning. The path to cybersecurity mastery begins with that first course, that first lab, and your commitment to protecting the digital world.
Eduard Kingly is a travel and lifestyle content creator with a focus on personal development and education. He combines firsthand travel experiences with research-driven insights to guide readers in discovering new places, building better habits, and pursuing meaningful learning.
1.In the realm of education-and-self-development, obtaining a certification such as CompTIA Security+ can offer professionals in cybersecurity a job market advantage, as the global demand for skilled cybersecurity professionals exceeds 3 million unfilled positions.
- For those aiming for a career move or advancement in the cybersecurity realm, obtaining a Chief Information Security Officer (CISO) certification like the Certified Information Systems Security Professional (CISSP) can provide a pathway to leadership and management roles, offering lucrative salaries and career flexibility.